Urgent iOS 16.6.1 Update Released: Protect Your iPhone from Spyware Attacks
Apple has urgently released iOS 16.6.1 to fix two critical iPhone vulnerabilities exploited in real-life attacks. Users must update immediately to protect their devices from spyware threats.
Apple Releases Urgent iOS 16.6.1 Update to Address Critical iPhone Vulnerabilities
Apple has just released iOS 16.6.1, and if you own an iPhone, you should apply this emergency update immediately. The reason for this urgency is that iOS 16.6.1 fixes two serious vulnerabilities in iPhones, both of which are already being actively exploited in real-life attacks.
Apple has intentionally kept the details of what's fixed in iOS 16.6.1 somewhat vague. This decision is aimed at ensuring that as many iPhone users as possible have the opportunity to update their devices before attackers can access the specific details of these vulnerabilities. However, it has been revealed that the flaws addressed in iOS 16.6.1 were exploited in real-life attacks to deliver spyware to targeted devices without requiring any interaction from the user.
The first vulnerability patched in iOS 16.6.1 is related to ImageIO, identified as CVE-2023-41064. This vulnerability could potentially allow malicious actors to execute code by exploiting a carefully crafted image. Apple has acknowledged that there is a report suggesting this issue may have already been actively exploited, underscoring the critical nature of this update.
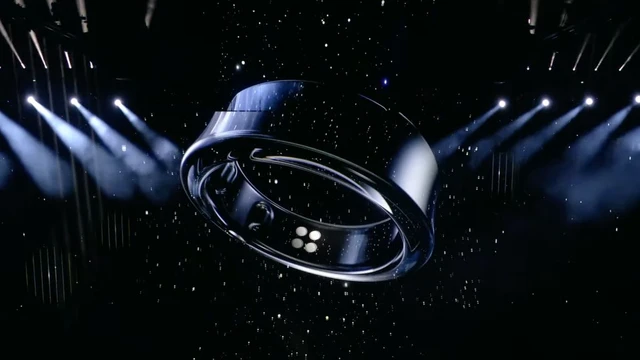
The second security issue addressed in iOS 16.6.1 pertains to a vulnerability within Apple's Wallet, tracked as CVE-2023-41061. This flaw could enable attackers to execute code through a maliciously crafted attachment. Once again, Apple has cautioned that there is evidence to suggest that this issue may have already been actively exploited.
The release of iOS 16.6.1 comes just ahead of the launch of iOS 17, expected within the next few weeks. Apple's decision to issue this emergency update indicates the severity of these vulnerabilities and the urgency to protect users from potential threats.
Over the past year, spyware like Pegasus has garnered significant attention for its increasing use in targeting iPhone users. This type of malware is particularly alarming because it grants attackers complete access to an iPhone, including encrypted applications like WhatsApp, allowing them to monitor and record the user's activities.
According to Citizen Lab, a cybersecurity organization, the two vulnerabilities addressed in iOS 16.6.1 were exploited specifically for delivering NSO Group's Pegasus spyware.
Citizen Lab discovered an actively exploited "zero-click" vulnerability, dubbed "BLASTPASS," during an investigation involving a device belonging to an individual associated with a Washington DC-based civil society organization with international ties. This attack had the capability to compromise iPhones running iOS 16.6 without requiring any action from the victim.
The exploit leveraged PassKit attachments containing malicious images sent from the attacker's iMessage account to the victim. These types of exploits are typically targeted at individuals with high threat profiles, such as public figures, government personnel, individuals targeted or harassed by nation-state actors, and journalists. The key distinction is that the attacker can carry out the attack without any action on the victim's part.
You might be wondering why Apple didn't release iOS 16.6.1 as a Rapid Security Response Update, a feature introduced in iOS 16 that enables Apple to deliver security-only updates quickly. However, a few months ago, Apple had to retract a Rapid Security Response update because it inadvertently caused other issues. This incident was a high-profile error, and it seems that Apple wanted to avoid a similar situation with the critical iOS 16.6.1 update.
In the realm of cybersecurity, the time between the discovery of exploited vulnerabilities and the application of patches is crucial. When details of vulnerabilities are made public, it creates an opportunity for more adversaries to exploit them and compromise iPhones.
Spyware is a particularly insidious form of attack because it allows attackers to gain covert access to an iPhone user's activities. Pegasus spyware, in particular, has been employed multiple times by nation-state attackers against high-profile targets. The method of delivering such attacks often involves sending a message containing a malicious image via iMessage, as seen in the case of the iOS 16.6.1 flaw. These attacks are termed "zero-click" because they require no interaction from the user.
Detecting and removing spyware from your device can be challenging. However, tools like iVerify can assist in identifying the presence of malware. Restarting your iPhone may disrupt spyware, although many users rarely perform this action.
For additional protection against spyware, Apple's Lockdown Mode can be enabled, especially if your iPhone is at a higher risk of being targeted. Keep in mind that this mode severely limits the functionality of your device, so it's best suited for situations where you believe you are a potential target.
Given the gravity of the vulnerabilities addressed, it is imperative that you update to iOS 16.6.1 without delay. While attacks exploiting these vulnerabilities are typically targeted, updating your device promptly is a crucial step in safeguarding your iPhone.
Security researcher Sean Wright emphasizes the importance of updating quickly, noting that even though attacks using these vulnerabilities are targeted, an urgent update is still essential. Additionally, it's worth checking and updating all your Apple devices, as the Wallet vulnerability fixed in iOS 16.6.1 is also present in Apple Watch, and the ImageIO issue has been addressed in a new Mac update.
iOS 16.6.1 is available for the iPhone 8 and later, iPad Pro, iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later.
To ensure your security, manually update to iOS 16.6.1, even if you have enabled automatic Apple updates. These updates are typically rolled out gradually to iPhones, so navigate to your iPhone's Settings General Software Update and promptly download and install iOS 16.6.1.
In conclusion, the release of iOS 16.6.1 underscores the critical nature of these vulnerabilities and the importance of staying vigilant and proactive in protecting your Apple devices from potential threats. Don't delay—update now to safeguard your iPhone and other Apple devices.
Download your fonts:
Polka Letter Stamp Font - Free Download
Frosty Holiday Font - Free Download
AEZ Vanity Font - Free Download
Deco Mon Type Font - Free Download
HeavyWeight Font - Free Download
Splashing Font - Free Download
BonesFont Font - Free Download












Comments